By Art Reisman
CTO, APconnections
www.netequalizer.com
To get started you’ll need to get ahold of two key software tools: 1) Ping Tool and 2) a Network Scan Tool, both which I describe in more detail below. And for advanced analysis (experts only), I will then show you how you can use a bandwidth shaper/sniffer if needed.
Ping Tool
Ping is a great tool to determine what your network responsiveness is (in milliseconds), identified by trying to get a response from a typical website. If you do not already know how to use Ping on your device there are hundreds of references to Ping and how to use it. Simply google “how to use ping ” on your favorite device or computer to learn how to use it.
For example, I found these instructions for my MAC; and there are similar instructions for Windows, iPhone, Linux, Android, etc.
- Open Network Utility (located inside Applications > Utilities).
- Click Ping.
- Fill out the “Enter the network that you want to ping” field. You can enter the IP address or a web URL. For example, enter http://www.bbc.co.uk/iplayer to test the ping with that website.
- Click Ping.
Network Scan Tool
There are a variety of network SCAN tools/apps available for just about any consumer device or computer. The decent ones will cost a few dollars, but I have never regretted purchasing one. I use mine often for very common home and business network issues as I will detail in the tips below. Be sure and use the term “network scan tool” when searching, so you do not get confusing results about unrelated document scanning tools.
Once you get your scan tool installed, test it out by selecting Network Scan. Here is the output from my MAC scan tool. I will be referencing this output later in the article.
Network Scan Output

Tip #1: Using Ping to see if you are really connected to your Network
I like to open a window on my laptop and keep Ping going all day, it looks like this:
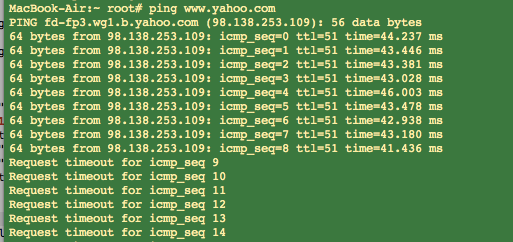
yahoo.com Ping Output
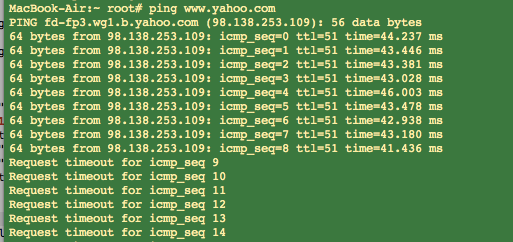
Amazingly, seemingly on cue, I lost connectivity to my Internet while I was running the tool for the screen capture above, and no, it was not planned or contrived. I kicked off my ping by contacting http://www.yahoo.com (type in “ping http://www.yahoo.com”), a public website. And you can see that my round-trip time was around 40 milliseconds before it went dead. Any ping results under 100 milliseconds are normal.
Tip #2: How to Deal with Slow Ping Times
In the case above, my Internet Connection just went dead; it came back a minute or so later, and was most likely not related to anything local on my network.
If you start to see missed pings or slow Ping Times above 100 milliseconds, it is most likely due to congestion on your network. To improve your response times, try turning off other devices/applications and see if that helps. Even your TV video can suck down a good chunk of bandwidth.
Note: Always test two public websites with a ping before jumping to any conclusions. It is not likely but occasionally a big site like Yahoo will have sporadic response times.
Note: If you have a satellite link, slow and missed pings are normal just a fact-of-life.
Tip #3: If you can’t ping a public site, try pinging your local Wireless Router
To ping your local router all you need to find is the IP address of your router. And on almost all networks you can guess it quite easily by looking up the IP address of your computer, and then replacing the last number with a 1.
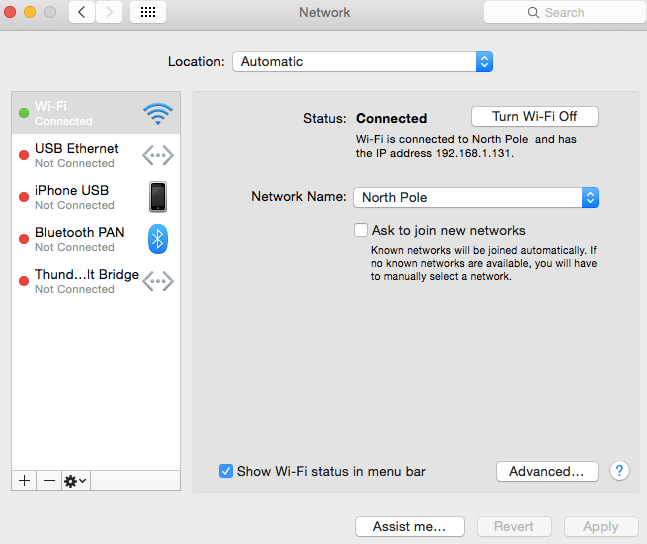
For example, on my computer I click on my little apple icon, then System Preferences, and then Networking, and I get this screen. You can see in the Status are it tells me that my IP address is 192.168.1.131.
Finding my IP address output
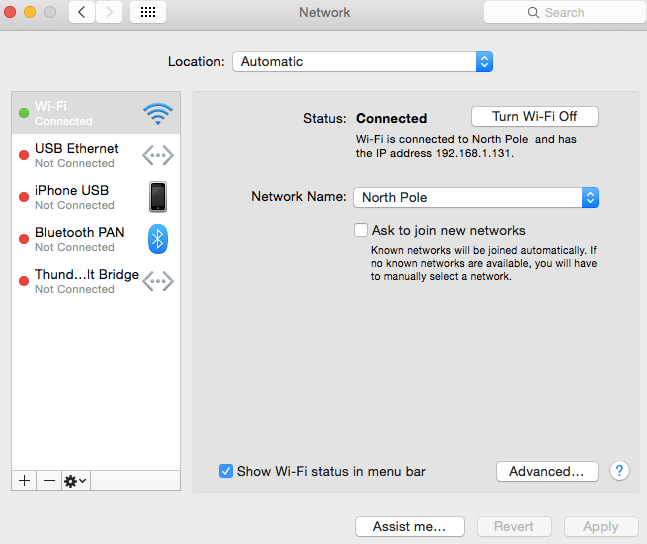
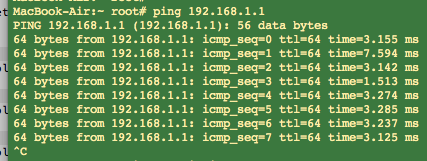
The trick to finding your router’s IP address is to replace the last number of any IP address on your network with a 1. So in my case, I start with my IP address of 192.168.1.131, and I swap the 131 with 1. I then ping using 192.168.1.1 as my argument, by typing in “ping 192.168.1.1”. A ping to my router looks like this:
Router Ping Output
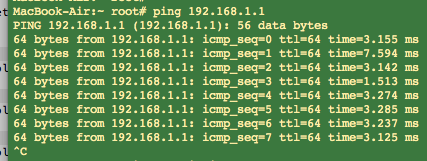
In the case above I was able to ping my local router and get a response. So what does this tell me? If I can ping my local wireless router but I can’t ping Yahoo or any other public site, most likely the problem is with my Internet Provider. To rule out problems with your wireless router or cables, I recommend that you re-boot your wireless router and check the cables coming into it as a next step.
In one case of failure, I actually saw a tree limb on the cable coming from the utility pole to the house. When I called my Internet Provider, I was able to relay this information, which saved a good bit of time in resolving issue.
Tip #4: Look for IP loops
Last week I was getting an error message when I powered up my laptop, saying that some other device had my IP address, and I determined that I was unable to attach to the wireless router. WHAT a strange message! Fortunately, with my scan tool I can see all the other devices on my network. And although I do not know exactly how I got into this situation, I was quickly able to find the device with the duplicate IP address and powercycle it. This resolved the problem in this case.
Tip #5: Look for Rogue Devices
If you never give out the security code to your wireless router, you should not have any unwanted visitors on your network. To be certain, I again turn to the scan tool. From my scan output, in the image above (titled “Network Scan Output” near the top of this post), you can see that there are about 15 devices attached to my network. I can account for all of them so for now I have no intruders.
Tip #6: Maybe it is just Mischief
There was a time when I left my wireless router wide open as I live in a fairly rural neighborhood and was just being complacent. I was surprised to see that one of my neighbors was on my access point, but which one?
I did some profiling. Neighbor to my west is a judge with his own network, probably not him. Across the street, a retired librarian, so probably not her. That left the Neighbor to my Southwest, kitty corner, a house with all kinds of extended family coming and going, and no network router of their own, at least that I could detect. I had my suspect. And I could also assume they never suspected I was aware of them.
The proper thing to do would have been to block them and lock my wireless router. But since I wanted to have a little fun, I plugged in my bandwidth controller and set their bandwidth down to a fraction of a Megabit. This had the effect of making their connection painfully dreadfully slow, almost unusable but with a ray of hope. After a week, he went away and then I completely blocked him (just in case he decided to come back!).
Tip #7: Advanced Analysis with a Bandwidth Shaper/Sniffer
If the Ping tool and the Scan tool don’t shed any light on an issue, the next step is to use a more advanced Packet Sniffer. Usually this requires a separate piece of equipment that you insert into your network between your router and network users. I use my NetEqualizer because I have several of them laying around the house.
Often times the problem with your network is some rogue application consuming all of the resources. This can be in the form of consuming total bandwidth, or it could also be seen as overwhelming your wireless router with packets (there are many viruses designed to do just this).
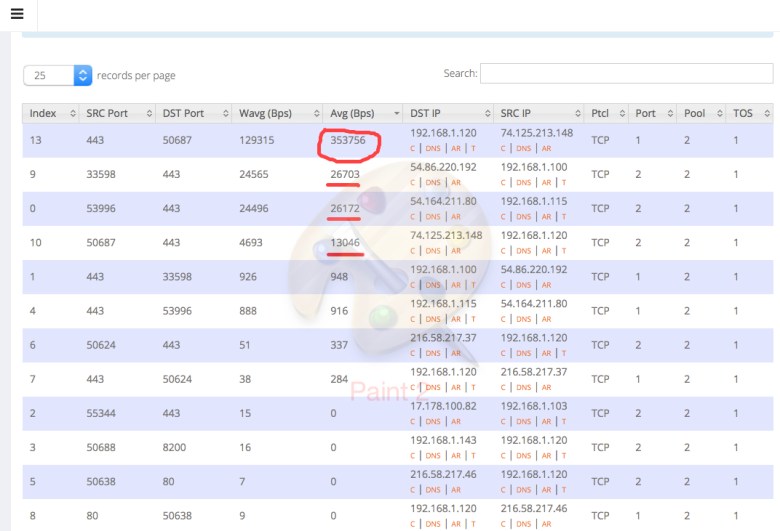
The image below is from a live snapshot depicting bandwidth utilization on a business network. 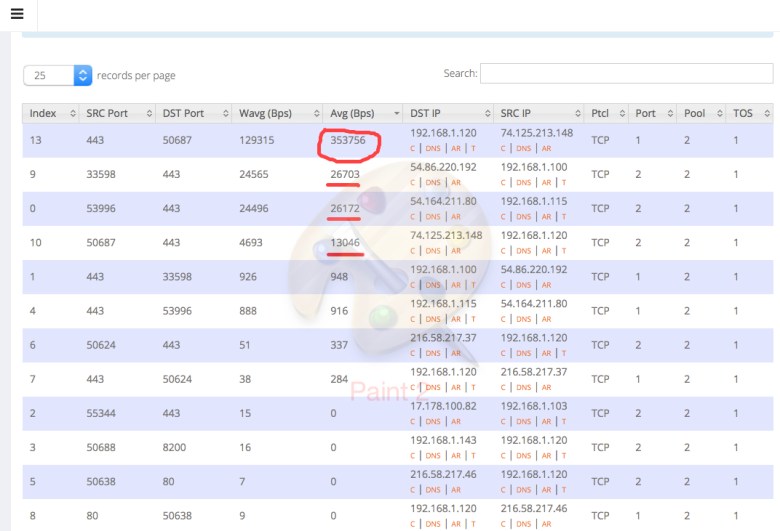
That top number, circled in red, is a YouTube video, and it is consuming about 3 megabits of bandwidth. Directly underneath that are a couple of cloud service applications from Amazon, and they are consuming 1/10 of what the YouTube video demolishes. On some lower cost Internet links one YouTube can make the service unusable to other applications.
With my sniffer I can also see total packets consumed by a device, which can be a problem on many networks if somebody opens an email with a virus. Without a sniffer it is very hard to track down the culprit.
I hope these tips help you to troubleshoot your network. Please let us know if you have any questions or tips that you would like to contribute.