| We hope you enjoy this month’s NetEqualizer Newsletter. Highlights include an update on the 8.5 Release, a reminder about our NetEqualizer Leasing program, a customer story about how RTR helped them identify a virus in their network, a refreshed NetEqualizer white paper, and more!
|

May 2017
|
|
8.5 Release – Development is Complete!
|
|
Greetings! Enjoy another issue of NetEqualizer News.
|
In this Issue:
:: First Impressions on our 8.5 Release
:: NetEqualizer Leasing always great option!
:: RTR Traffic History Reports Capture Unknown Virus Activity for WNPL
:: Updated Executive White Paper
:: Best of Blog: How to Create and Send an Encrypted File With No NSA Backdoor
| First Impressions on our 8.5 Release |
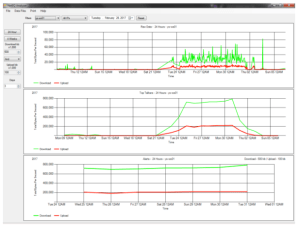
8.5 Release Development is Complete!I finally got a chance to kick the tires on our 8.5 release, and it kicked me back! I really like so much in 8.5, it is difficult to determine where to start! The biggest wow factor to hit me was our enhanced DNS reporting. For years our customers have been asking, “Can you tell me how much traffic went to YouTube or Netflix?” Well, I am thrilled to say that finally the answer is yes. With our DNS reporting you can now track all the data to any well-known public domain. The screen shot below of our Active Connections Report says it all. You can see the domains in the DST (destination) and SRC (source) columns for all live traffic flowing through the network.
In addition to being able to see public domains for all active traffic, you can now also view Traffic History for any host names that you have set up to track. You can see history for a selected public domain in the screenshot below.
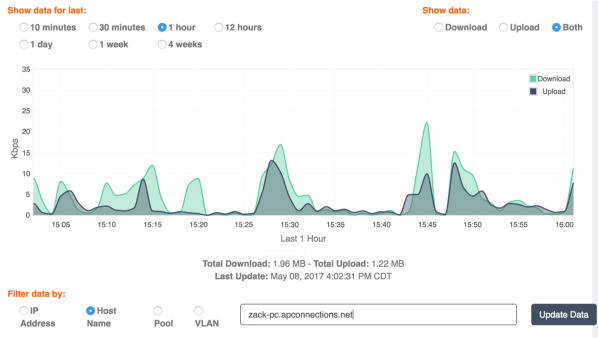
I also love our expanded login capabilities. Many of our customers have a support Help Desk team on site. These are the first responders for network problems in your organization. Just like their counterparts in the medical field (EMTs), they may not be trained in advanced surgical techniques. For example, you would not want them making policy changes on your bandwidth controller, but you definitely need your help desk personnel to do some initial triage, gather some data, and keep the patient alive, until the doctor arrives on scene. Our NEW Read Only login will give them access to RTR and all its advanced reporting screens, without the possibility of any life-threatening policy changes to the network. You can see that this person is logged in as Read Only by looking in the top right portion of the menu bar for the RTR icon, or looking for the “report” login next to the new Logout feature.
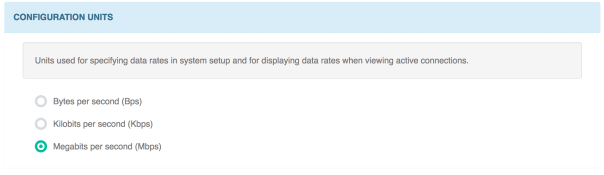
And finally, we continue to expand our Preferences capabilities, so that you can customize your experience with the NetEqualizer. “Remember one hundred and twenty eight thousand bytes per second is a Megabit.” I was getting tired of uttering this phrase and being an apologist for our units displayed on our connection tracking (Active Connections) screen. In fairness to our engineering team, the connection tracking table started out as a simple troubleshooting tool for internal use, and has now morphed into one of the more important real-time reporting screens for our customers. With 8.5 we bring you units in Megabits (or whatever unit your preference may be)! See the screenshot below. Once you select your preference, these units will be on your Active Connections Report.
With our 8.5 release entering the system test phase, we will soon be looking for Beta Testers (June/July timeframe). If you are interested in participating, please contact us. |
| NetEqualizer leasing always a great option! |
Check out our leasing program!Do you have a short term need for a bandwidth shaper? Perhaps a conference event, or something to tide you over while waiting for a bandwidth upgrade? Maybe your business model requires you to spread out expenses over time instead of an up front purchase? If you answered yes to one or more of these questions, now is the time to contact us about leasing a NetEqualizer. We offer leases starting at 2 months with no long term contract. |
| RTR Traffic History Reports Capture Unknown Virus Activity for WNPL |
| Updated Executive White Paper |
Take a look at our refreshed white paper…Our Executive White Paper has been updated to highlight a key capability of the NetEqualizer – that we are able to shape both encrypted and unencrypted traffic. This is an important advantage of behavior-based shaping. Application traffic shapers are only able to shape unencrypted traffic, as they need to classify it to work with it. We have also updated the Comparison Table on Page 2 to better highlight how the NetEqualizer compares to Other Traffic Shapers. The Executive White Paper is a good summary for management to read to get a quick feel of the NetEqualizer’s core capabilities, and also to understand how it differs from traditional application shapers. Read our updated Executive White Paper here… |
| Best Of Blog |
How to Create and Send an Encrypted File with No NSA BackdoorBy Art Reisman
Note: Believe it or not in a previous life, before I settled on computer science, I was a math major. Not much stuck from those days but I did remember one lesson very well, and that was that there are a plethora of ways to implement a mathematic encryption of data. In the following blog article I share with you an easy to use a program for personal encryption. Below is a little routine I wrote to encrypt and decrypt a file. This script is meant for encrypting text files and sending them privately through e-mail as an attachment. Note: The author makes no claims about whether this encryption technique can be broken. It would not be easy. Here is what you need to use this program. |
| Photo of the Month |
 Kansas Prairie Home from Days Gone By…
One of our staff members was visiting western Kansas recently, and decided to take a bike tour. This house is one of many that remain from the Dust Bowl days, when many farmers abandoned their homes due to the prolonged severe drought. These homes dot the land, much of which was given away by the Homestead Acts. |
| APconnections, home of the NetEqualizer | (303) 997-1300 | Email | Website |



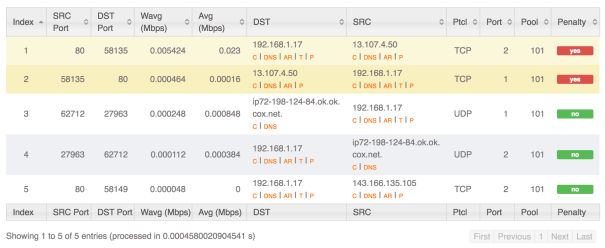
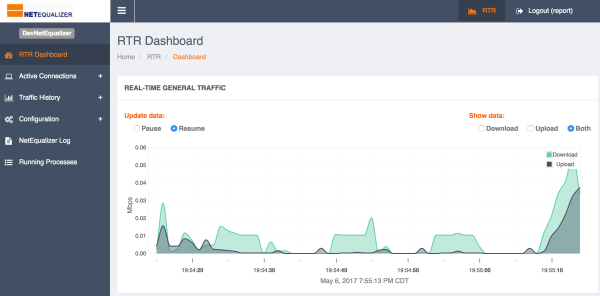



 Once the IP’s were resolved to DNS names, I was surprised to see such high bandwidth from a specific PC. Bandwidth that was large and during closed office hours spreading across multiple days. I approached the user to see if they had any experience with slow or intermittent internet access and sure enough they did. Their experience of slowness was the NetEQ doing it’s wonderful job of penalizing them and normally it should, but the user experienced slowness due to a bug on the computer. They also stated they left their PC on overnight because they didn’t want to lose what they had been working on, so this explained why the traffic showed during closed hours. When asked if they knew when they started to experience slowness, their answer matched what the data showed in the four week report.
Once the IP’s were resolved to DNS names, I was surprised to see such high bandwidth from a specific PC. Bandwidth that was large and during closed office hours spreading across multiple days. I approached the user to see if they had any experience with slow or intermittent internet access and sure enough they did. Their experience of slowness was the NetEQ doing it’s wonderful job of penalizing them and normally it should, but the user experienced slowness due to a bug on the computer. They also stated they left their PC on overnight because they didn’t want to lose what they had been working on, so this explained why the traffic showed during closed hours. When asked if they knew when they started to experience slowness, their answer matched what the data showed in the four week report.